Intel processors need hardware fixes due to new LVI attack
Security experts discovered a new attack on Intel processors called Load Value…
Information security experts said that AMD processors are vulnerable to two attacks
A joint group of specialists from the National Center for Scientific Research…
More than 40% of Android users are at risk of cyberattacks
According to a study by Which company, more than 40% of active…
Researchers found about 700 problematic Microsoft subdomains
Vullnerability researchers found about 700 problematic Microsoft subdomains and captured one of…
Malicious Ledger Live extension for Chrome steals Ledger wallet data
Harry Denley, Director of Security in MyCrypto discovered the malicious Ledger Live…
Chinese coronavirus detection app transmits data to the police
Last month, Chinese authorities released the Alipay Health Code coronavirus detection application,…
Cyberattack with the use of ransomware forced Epiq Global to shut down its systems
Epiq Global, a large international law firm, has become the victim of…
Vulnerability in OAuth Protocol Allows Hacking Any Facebook Account
The vulnerability is contained in the Facebook login feature, which uses the…
Hackers scan network for vulnerable Microsoft Exchange servers
Information security experts warn that hackers are already scanning the network for…
Kr00k Wi-Fi-chips vulnerability affects over a billion devices
At the RSA 2020 conference, ESET specialists spoke about the new Kr00k…
Almost three quarters of modern phishing sites use SSL
Anti-Phishing Working Group (APWG) experts in their new report on this cyber…
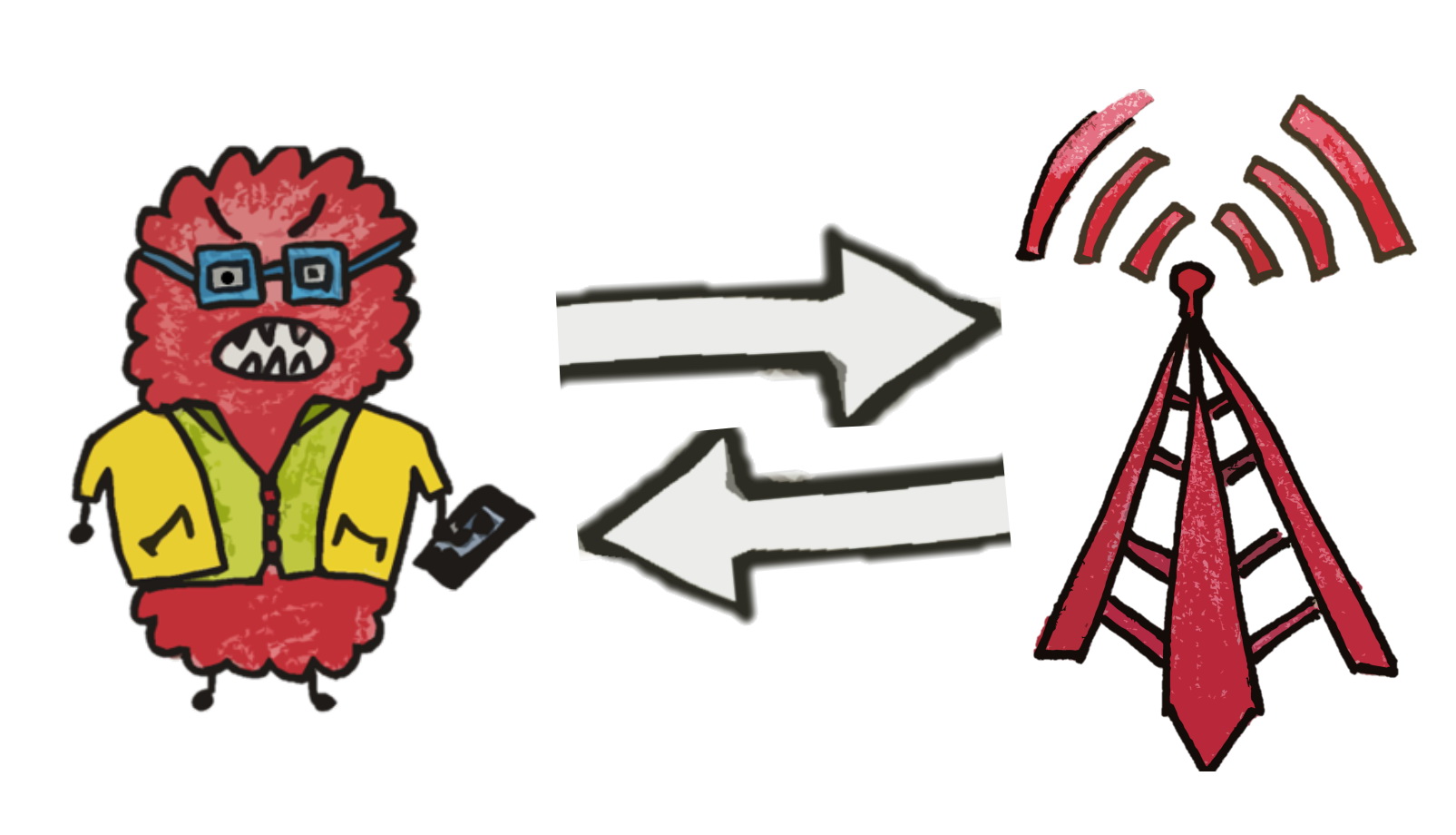
IMP4GT Vulnerability in LTE Threatens Almost All Modern Smartphones
Experts from Ruhr University reported an IMP4GT (IMPersonation Attacks in 4G NeTworks)…