FBI and NSA release a statement about attacks by Russian hackers
The FBI and NSA claim that a group of Russian government hackers are brute-forcing companies and organizations around the world. The NSA, the Department of Homeland Security (DHS CISA), Cybersecurity…
Cybersecurity specialists released a free decryptor for Lorenz ransomware
Dutch company Tesorion has released a free decryptor for data affected by Lorenz ransomware attacks. Now some files can be recovered for free, without paying the ransom. Rijnders said the…
Exploit for dangerous PrintNightmare problem in Windows has been published online
A PoC exploit for the dangerous PrintNightmare vulnerability in Windows Print Spooler (spoolsv.exe) has been published online. This bug has ID CVE-2021-1675 and was patched by Microsoft just a couple…
Babuk Locker ransomware builder leaked into the network
The Babuk Locker ransomware builder has appeared in the public domain. With its help anyone can design its own ransomware, the well-known information security expert Kevin Beaumont said on Twitter.…
Clop ransomware continues to work even after a series of arrests
The media reported that Clop ransomware continues to work: its operators have again begun posting data stolen from victims on their website. The fact is that last week, as a…
John McAfee, creator of McAfee antivirus, found dead in prison in Barcelona
On June 23, 75-year-old programmer and creator of the first commercial antivirus McAfee John McAfee passed away - he was found dead in his cell in the Barcelona prison "Briens-2".…
Previously assessed as insignificant, DirtyMoe botnet infected over 100,000 Windows systems
The developers of the DirtyMoe botnet (which was assessed as insignificant) added to it a worm-like spreading module, after which the malware infected more than 100,000 Windows systems. The DirtyMoe…
Encryption algorithms for 2G networks have been intentionally weakened
A group of scientists from several European universities published a report on encryption algorithms for 2G networks, which many information security experts and the media have already called sensational. The…
Cyber police of Ukraine arrested persons linked with the Clop ransomware
As a result of a joint operation carried out with the assistance and coordination of Interpol by law enforcement agencies and the cyber police of Ukraine, South Korea and the…
Russian-speaking hackers attacked the government infrastructure of Poland
The Sejm of Poland will hold a secret meeting, at which the government will hear information about the recent attacks by Russian-speaking hackers on the government infrastructure of Poland and…
Google stopped trying to shorten URLs in the address bar
Google's experiment with attempt to shorten URLs (hiding parts of the URL from the address bar) has finally failed and was finished. Let me remind you that in recent years,…
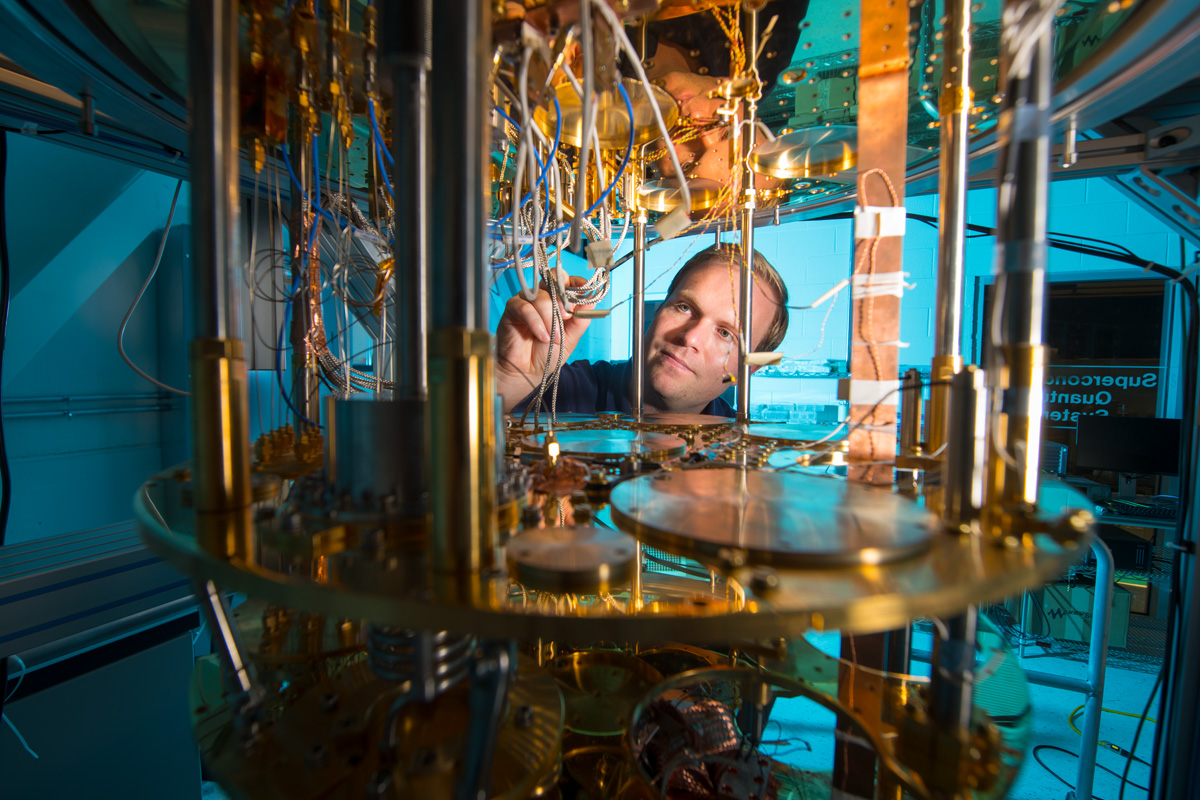
Quantum computers will be able to hack bitcoin wallets
Experts argue that quantum computers will be able to hack bitcoin wallets, but the most advanced cryptographers are in a hurry to find protection. While quantum computing is still in…