Tips & Tricks
DDoS-For-Hire Services Used by Hacktivists in 2023
Most people think you must be a hacker to participate in cyberattacks. However, as the last year has shown, downloading…
US Authorities Warn of Disaster-Related Scams
Following natural disasters and severe weather, there is a higher chance of fraudulent activities as scammers prey on vulnerable individuals…
ChatGPT Causes New Wave of Fleeceware
Artificial intelligence is one of the most significant advances in technology. It is used in one way or another everywhere,…
Oneetx.exe – What is that process? Oneetx Removal
Oneetx.exe is a malicious process, related to Amadey dropper malware. It can be spectated in the Task Manager, with seemingly…
PyPI Malware Storm Forces to Suspend New Uploads
Python Package Index, a software repository for Python developers, recently faced a massive attack. An enormous flow of malicious uploads…
10 Types of Cyber Security Attacks in IoT
In a world where information progress is rapidly developing, it is impossible to do without IoT. You probably don’t know what you’re talking about, so let’s take a quick look…
Penetration Testing: Stages and Methods
What is penetration testing? Penetration testing is a method by which the security of computer systems and networks can be assessed by simulating a hacker’s attack. It is possible to…
VPN, Proxy, or Tor: Differences, Meaning
You’ve probably heard the words VPN, Proxy, and Tor. You may even regularly use these technologies to remain anonymous, bypass blockades, view content blocked in your region, or simply access…
Difference Between Polymorphic and Metamorphic Viruses
Polymorphic and Metamorphic Malware: the Comparison In this article, we consider two types of pests: polymorphic and metamorphic viruses, which were designed to destroy the integrity of the operating system…
TOP DNS Attacks Types
What is a DNS (Domain Name Server) Attack? A DNS attack is the situation when an attacker either attempts to compromise a DNS network or uses its inherent attributes to…
Difference Between Phishing and Pharming
Intruders try to keep up with the development in the digital world. The technology seeks to provide users with more effective resources, but the attackers in turn try to come…
Smishing And Vishing: Differences To Know About Phishing Attacks
You can say it has become much easier for various criminals to get to their victims and target them with different schemes. And all because of the ubiquitous internet these…
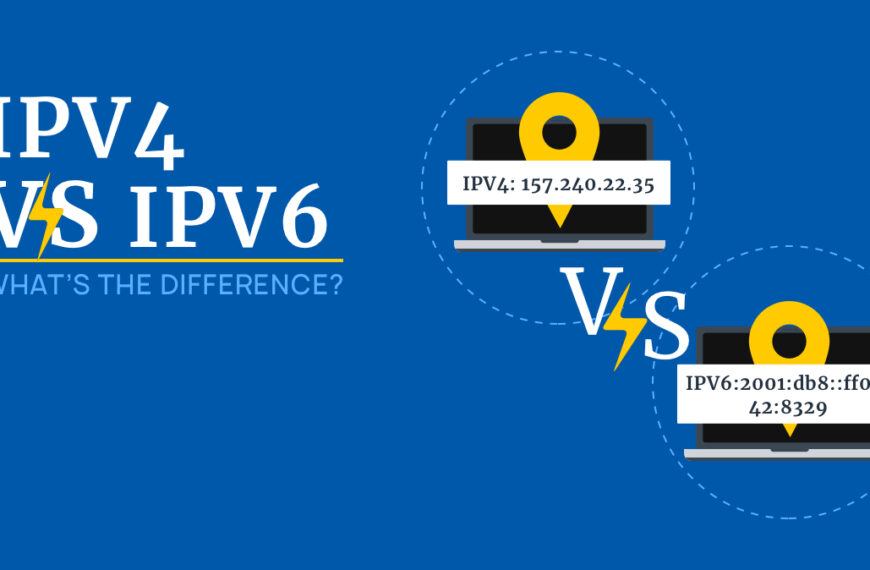
IPv4 vs IPv6: What’s the Difference?
What is IPv4 and IPv6? IP addresses allow computers and devices to communicate over the Internet. Without them, no one would know who is saying what and to whom. But…
Tips For You To Recognize Fake Hacking
Fake hacking is a provocation or hacking that presupposes and notifies that someone has hacked the system. The purpose of this attack is to deceive the user and get money…
Is It Safe to Use a Password Manager in 2022?
What’s the Idea Behind Password Managers? In the cybersecurity world, everyone knows that passwords are real. It’s only in the movies hackers can effortlessly detour or hack passwords. A strong…
Dangerous Injection Attacks
Today, Injection attacks are a significant problem and top the list of vulnerabilities. There are good reasons for this. They are dangerous. Injection attacks exploit various vulnerabilities to deliver untrusted…
Top Types of Spoofing Attacks
Spoofing 1 is a kind of cybercrime in which attackers…