The Security Blog From Gridinsoft
New Acer Breach Exposes 160GB of Data
Companies tend to hide the case of a cybersecurity breach – for certain reasons, it may be for their good.…
BlackLotus UEFI Bootkit Bypasses Protection even in Windows 11
ESET experts reported that the BlackLotus UEFI bootkit, which is sold on hacker forums for about $ 5,000, is indeed…
New stealthy “Beep” malware focuses heavily on evading detection
Cybercriminals periodically develop something new. Sometimes it is an updated version of already known malware, and sometimes it is something…
LastPass Breach Investigation Goes On, Things are Even Worse
LastPass, owned by GoTo (formerly LogMeIn) and with over 30 million users, revealed new details about the cyber incidents that…
YouTube Video Causes Pixel Smartphones to Reboot
Users have found that Pixel smartphones powered by Google Tensor processors are rebooting when user is trying to watch a…
Researcher Published PoC Exploit for ProxyLogon Vulnerabilities in Microsoft Exchange
An independent information security researcher from Vietnam has presented a PoC exploit for ProxyLogon vulnerabilities in Microsoft Exchange, whose viability has already been confirmed by such well-known experts. Last week,…
Hackers gained access to surveillance cameras in Tesla, Cloudflare and banks
Bloomberg reports that some hackers have gained access to surveillance cameras installed in Tesla, Equinox, medical clinics, prisons and banks. In addition to the images from the cameras, the hackers…
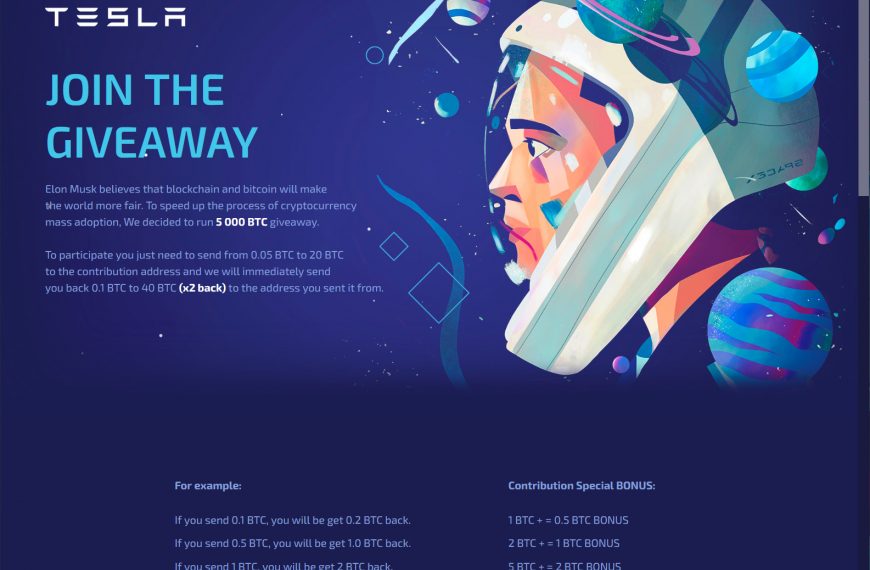
Dogecoin scam: send credentials and pay $300
Dogecoin scam is just a part of the online fraud which is spreading massively these days. It may have an impact on your wallet, as well as on your private…
Hackers attacked Microsoft Exchange servers of the European Banking Authority
Hackers attacked the servers of the Microsoft Exchange European Banking Authority (EBA). Due to the attack, EBA had to temporarily shut down its mail systems as a precaution. EBA launched…
Expert intercepted windows.com traffic using bitsquatting
An independent expert known as Remy discovered that Microsoft domains were not protected against bitsquatting and intercepted windows.com traffic. The expert conducted his experiments on the example of the windows.com…
The expert told how he hacked into a nuclear power plant
Charles Hamilton, the chief security expert of the SpiderLabs team from the information security company Trustwave, described how he hacked into a nuclear power plant. In cybersecurity, the worst-case scenario…
Facebook virus: checking the details
Facebook virus is a common (and partially misguiding) name for spam messages in Facebook. These notifications are spread from accounts of your “friends” on Facebook. Don’t misunderstand. They didn’t become…
Microsoft has released emergency patches for Exchange
Microsoft has released emergency patches for four 0-day vulnerabilities found in the code of the Exchange mail server (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065). The company warned that Chinese hackers from…
Google membership rewards scam: explaining the details.
Google membership rewards scam is a new popular type of online fraud. This page opens absolutely spontaneously, and says you got a valuable prize. With different techniques, fraudsters force you…
Full-fledged exploits detected for Specter vulnerability
French cybersecurity specialist Julien Voisin reported that in early February 2021, someone uploaded exploits for the Specter vulnerability to VirusTotal. This is the first time that a “combat” exploit for…
Hackers used Firefox extension to hack Gmail
Proofpoint discovered a campaign in which hackers used a Firefox extension to hack Gmail. The attacks were linked to the Chinese group TA413. According to the researchers, the campaign was…
In LastPass for Android found seven built-in trackers
German cybersecurity expert Mike Kuketz noticed that the LastPass Android app has seven trackers that monitor users. The researcher builds his findings on the report of the non-profit organization Exodus,…