The Security Blog From Gridinsoft
Researcher Publishes RCE Exploit for Critical Vulnerability in Microsoft Word
A proof-of-concept exploit for the CVE-2023-21716 vulnerability in a Microsoft Office product, namely Microsoft Word, has emerged online. This issue…
Bing Chatbot Could Be a Convincing Scammer, Researchers Say
Security researchers have noticed that by using text prompts embedded in web pages, hackers can force Bing’s AI chatbot to…
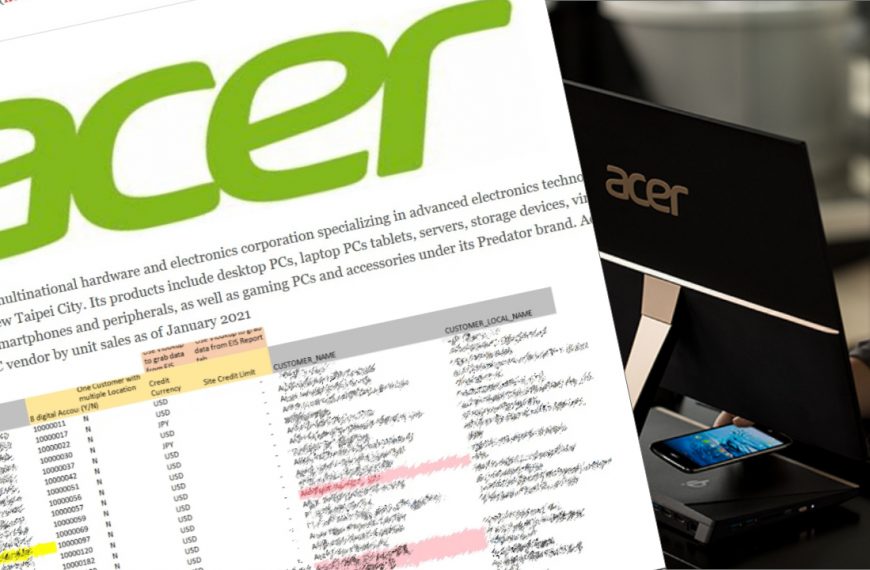
New Acer Breach Exposes 160GB of Data
Companies tend to hide the case of a cybersecurity breach – for certain reasons, it may be for their good.…
BlackLotus UEFI Bootkit Bypasses Protection even in Windows 11
ESET experts reported that the BlackLotus UEFI bootkit, which is sold on hacker forums for about $ 5,000, is indeed…
New stealthy “Beep” malware focuses heavily on evading detection
Cybercriminals periodically develop something new. Sometimes it is an updated version of already known malware, and sometimes it is something…
Attackers using DCCP protocol for DDoS attacks
Akamai has noticed that attackers are using the little-known DCCP network protocol (Datagram Congestion Control Protocol) for DDoS attacks. This internet standard was approved in 2007 and helps monitoring network…
Check Point: Desperate Job Seekers Are Ready To Work For Cybercriminals
CheckPoint experts found that the number of job search ads on the darknet and on hacker forums is growing – job seekers that were desperate to find a job are…
REvil ransomware operators attacked Acer and demand $50,000,000
The REvil ransomware attacked the Taiwanese company Acer (the sixth-largest computer manufacturer in the world, accounting for about 6% of all sales). Cybercriminals are demanding from the manufacturer $50,000,000, which…
Russian who tried to hack Tesla was pleaded guilty
The Russian, who offered a Tesla specialist $1,000,000 for installing malware into the company’s network in Reno, Nevada, was pleaded guilty. In August 2020, we talked about the arrest of…
DTLS can amplify DDoS by 37 times
Netscout warns that using of the DTLS vector allows hackers to amplify DDoS attacks by 37 times. The researchers found that criminals are using a relatively new vector for amplifying…
REvil spokesman boasts that hackers have access to ballistic missile launch systems
A Revil representative under the pseudonym Unknown, claims that the hackers, partners in the use of malware, have access to ballistic missile launch systems. Cybercriminal group REvil operates on the…
Microsoft Introduces One-Click ProxyLogon Fix Tool
Microsoft developers have released a tool called EOMT (Exchange On-premises Mitigation Tool) designed to install updates on Microsoft Exchange servers and one-click ProxyLogon vulnerabilities fix. The utility is already available…
Google experts published PoC exploit for Specter that is targeting browsers
Google engineers published a PoC exploit to demonstrate the effectiveness of using the Specter vulnerability in browsers to access information in memory. This PoC exploit is reported to work with…
GitHub removed ProxyLogon exploit and has been criticized
The administration of the GitHub service has removed a real working exploit for the ProxyLogon vulnerabilities in Microsoft Exchange, though information security specialists have sharply criticized GitHub. Yesterday we wrote…
Researcher Published PoC Exploit for ProxyLogon Vulnerabilities in Microsoft Exchange
An independent information security researcher from Vietnam has presented a PoC exploit for ProxyLogon vulnerabilities in Microsoft Exchange, whose viability has already been confirmed by such well-known experts. Last week,…
Hackers gained access to surveillance cameras in Tesla, Cloudflare and banks
Bloomberg reports that some hackers have gained access to surveillance cameras installed in Tesla, Equinox, medical clinics, prisons and banks. In addition to the images from the cameras, the hackers…
Dogecoin scam: send credentials and pay $300
Dogecoin scam is just a part of the online fraud which is spreading massively these days. It may have an impact on your wallet, as well as on your private…